 March 3, 2026 by Editor |
March 3, 2026 by Editor |
The Imperative of Zero-Trust Security in Modern Corporate Communications
In Singapore’s competitive corporate landscape, the quarterly town hall or all-hands meeting is no longer a simple internal communication. It is a critical strategic event, often involving the dissemination of sensitive financial data, unannounced product roadmaps, and confidential M&A discussions. For hybrid events, where key stakeholders and remote teams join virtually alongside a physical audience, the attack surface for data interception expands exponentially. Standard streaming solutions, often relying on basic platform-level security, present an unacceptable risk for any organization governed by Singapore’s Personal Data Protection Act (PDPA) or handling market-sensitive information. The conversation must therefore shift from basic stream security to a comprehensive, broadcast-grade, end-to-end encryption (E2EE) strategy. This is not merely an IT function; it is a core component of modern production workflow, demanding a deep understanding of signal flow, transport protocols, and network architecture to ensure the integrity and confidentiality of the entire communication chain, from the camera lens to the corporate viewer’s screen.
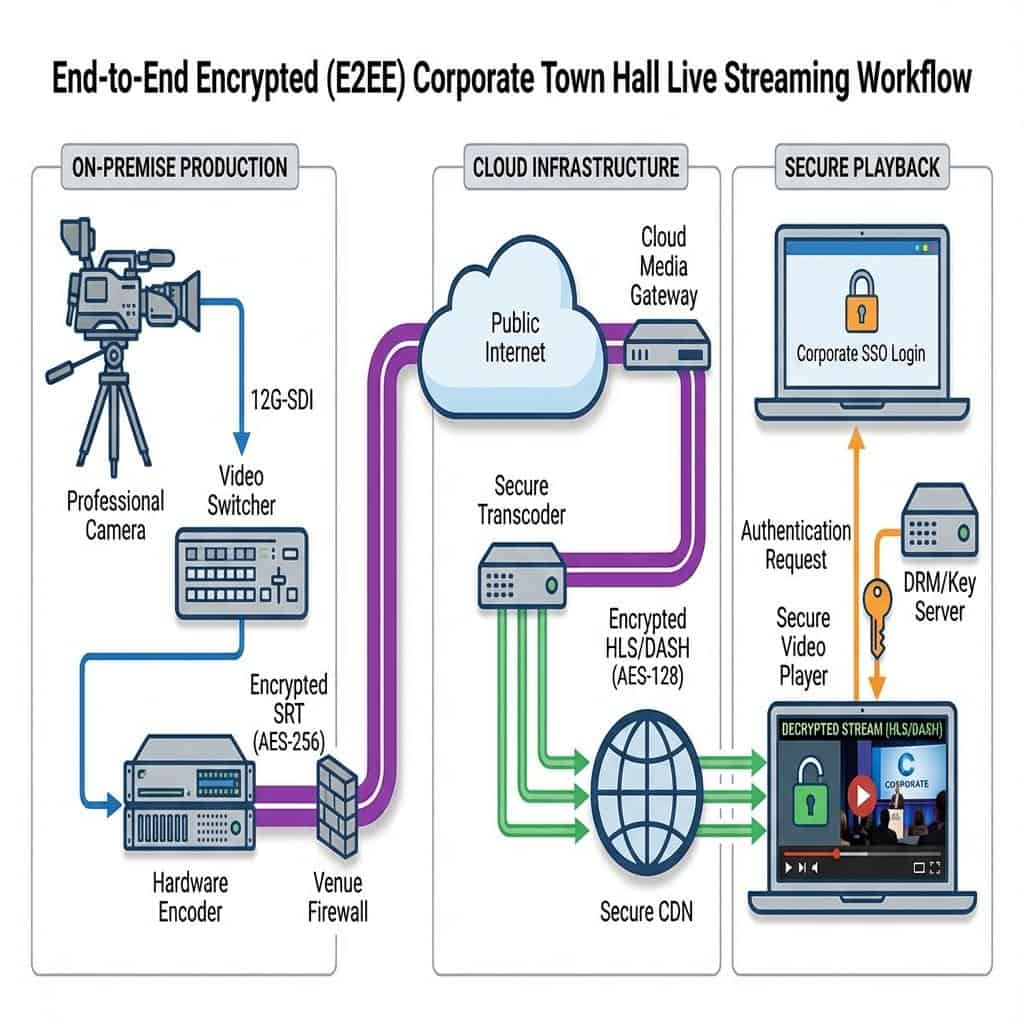
True E2EE in a professional B2B live production context means the video and audio data is encrypted at the point of origin, the hardware encoder, and remains encrypted throughout its entire journey across contribution networks, cloud processing infrastructure, and content delivery networks (CDNs). Decryption occurs only at the endpoint, inside the authenticated viewer’s secure video player. This zero-trust model assumes that any network segment could be compromised, rendering intermediary transcoding or processing points incapable of accessing the unencrypted content payload. For event planners and IT directors in Singapore, implementing this level of security is fundamental to mitigating risks of industrial espionage, reputational damage, and regulatory penalties. It requires moving beyond consumer-grade platforms and adopting a professional broadcast engineering mindset focused on signal integrity and cryptographic security at every stage of the production and delivery workflow.
Deconstructing the E2EE Signal Chain in a Hybrid Production Environment
Achieving robust E2EE is not a single software setting; it is a chain of custody for your data, built with specific hardware, protocols, and architectural decisions. Each link in this chain must be secured, starting from the moment the signal is generated in the event venue. A vulnerability at any point can compromise the entire workflow, regardless of how secure other segments are.
On-Premise Acquisition: Securing the Source Signal
The E2EE workflow begins inside the venue, at the point of signal acquisition. The uncompressed baseband video signals, typically transported from cameras to the production switcher via 12G-SDI or 6G-SDI cabling for 4K/UHD resolutions, are inherently insecure within the local production environment. The same applies to audio, whether it’s analog XLR or a networked audio-over-IP protocol like Dante. While the physical security of the venue is the first line of defense, the critical point for E2EE is the interface between the main program feed output from the video switcher, like a Blackmagic ATEM Constellation or Ross Carbonite, and the primary contribution encoder. This program feed, a pristine mix of all video and audio sources, is handed off to a dedicated hardware encoder. It is within this device, before the signal ever traverses an external network, that the first stage of encryption must occur. This ensures that even the on-premise network path from the encoder to the edge firewall is carrying a protected stream.
Contribution Encoding and Secure Transport Protocols
The choice of transport protocol is the most critical decision in the E2EE signal chain. The legacy Real-Time Messaging Protocol (RTMP) is inadequate for secure, high-quality contribution. While its secure variant, RTMPS, wraps the stream in a Transport Layer Security (TLS) tunnel, it lacks the robust error correction and low-latency performance required for professional broadcast. The industry standard for secure contribution is now Secure Reliable Transport (SRT). Developed by Haivision, SRT is an open-source protocol that provides AES-128 or AES-256 bit encryption for the video and audio payload. Its security model is based on a pre-shared key (PSK) and a secure handshake mechanism. Before any media is transmitted, the SRT encoder and the downstream SRT gateway or server exchange credentials. Only with the correct key can the receiving end decrypt the stream. Furthermore, SRT offers superior performance over unstable networks, using packet retransmission to correct for network jitter and packet loss, ensuring a high Quality of Service (QoS) for the encrypted feed. A typical configuration for a high-stakes town hall would be a 1080p50 stream encoded as H.265 (HEVC) at 8-10 Mbps, encapsulated in an SRT stream with AES-256 encryption, sent from a hardware encoder like a Haivision Makito X4 or an AJA HELO Plus.
The Cloud Ingest and Processing Stage
Once the encrypted SRT feed leaves the venue’s network, it travels to a cloud media server or ingest point. In a true E2EE workflow, this server acts as a pass-through or a transcoder that operates on the encrypted payload without ever decrypting it. The SRT stream is received, and its encrypted contents are repackaged into adaptive bitrate (ABR) formats like HLS (HTTP Live Streaming) or MPEG-DASH for delivery. Critically, the encryption is maintained. The content segments for HLS/DASH are themselves encrypted, typically using AES-128. The decryption keys for these segments are managed by a separate key server, and access to these keys is tightly controlled. This ensures that the video assets stored on the cloud origin server or CDN are fully protected. Unauthorized access to the video files is useless without the corresponding decryption keys, which are only delivered to authenticated end-users during playback.
Implementing a Zero-Trust Architecture for Production and Delivery
A zero-trust security model, which assumes no user or device is trusted by default, is essential for protecting high-value live events. This requires meticulous network design, secure integration points for remote participants, and a reliance on enterprise-grade hardware that is purpose-built for secure, high-availability streaming operations.
Network Segmentation and Access Control
The on-site production network must be logically and physically isolated from any other network, including venue Wi-Fi or the client’s corporate LAN. This is achieved by creating a dedicated Virtual LAN (VLAN) for all production equipment: cameras, switchers, encoders, audio mixers, and control surfaces. A strict firewall policy should be implemented at the edge of this VLAN, permitting only the required outbound traffic for the SRT stream on its designated UDP port and blocking all other inbound and outbound connections. IP whitelisting should be used to ensure the contribution encoder can only connect to the specific IP address of the cloud ingest server. For added security, production devices should be configured with static IP addresses, and any unused network ports on switches should be disabled. This principle of least privilege prevents lateral movement across networks in the event a single production device is compromised.
Securing the Hybrid Integration Point
Integrating remote speakers from platforms like Microsoft Teams or Zoom into a high-end broadcast is a common requirement for hybrid town halls, and it presents a significant security challenge. Simply screen-capturing a laptop is not a professional or secure solution. The correct approach involves using dedicated hardware that can securely bring these remote feeds into the production environment. One method is using a system that can join a Teams meeting as a participant and provide a clean, isolated 3G-SDI output for that feed, which can then be ingested into the main video switcher. Another powerful workflow utilizes Network Device Interface (NDI). Newer versions of NDI offer encryption capabilities. A remote source can be converted to NDI on a secure machine, and that encrypted NDI stream can be brought into the production network via an NDI gateway, where it is decoded back to SDI. This process ensures the remote contribution feed is isolated and securely transported into the primary production switcher without exposing the core production network to the public internet.

The Role of Dedicated Hardware Encoders
While software encoders are flexible, for high-stakes E2EE workflows, dedicated hardware encoders are non-negotiable. Enterprise-grade rackmount encoders from manufacturers like Haivision, Kiloview, or Matrox are designed for 24/7 reliability and have dedicated processing chips (ASICs) for real-time video encoding and encryption. This hardware-level processing ensures stable performance and minimal latency, which is crucial for live events. More importantly, these devices have hardened operating systems that are less vulnerable to the malware and security threats that affect general-purpose computers. They provide robust implementations of SRT with full support for AES-256 encryption and detailed connection logging for security audits. Their physical SDI and professional audio inputs ensure signal integrity from the production switcher, completing the secure chain from acquisition to contribution.
E2EE Delivery and Playback: Securing the Final Mile
Encrypting the contribution feed is only half the battle. The security model must extend all the way through the delivery infrastructure to the end-user’s device. This final mile of delivery is where many security strategies fail, as they often rely on generic, public-facing video players and open CDNs.
Content Delivery Network (CDN) Security Features
The choice of CDN is critical. An enterprise-grade CDN will offer multiple layers of security for the final delivery stream. URL tokenization, also known as signed URLs, is a fundamental feature. This process generates a unique URL for each viewing session that includes a cryptographic token and an expiration time. This prevents URL hijacking and unauthorized sharing of the stream link. Geo-fencing and IP whitelisting/blacklisting at the CDN level allow for precise control over who can access the stream, restricting it to specific geographic regions or corporate IP address ranges. For the highest level of browser-based security, Digital Rights Management (DRM) integration is necessary. Technologies like Google Widevine, Apple FairPlay, and Microsoft PlayReady provide license-based, hardware-level decryption within the browser or native application, offering the strongest possible protection against screen recording and content piracy.
Player-Side Decryption and Secure Viewing Environments
The final decryption must occur on the client device. This requires an enterprise video player that can handle the secure key exchange process for the encrypted HLS/DASH stream. The viewing experience should be hosted on a secure web portal that requires user authentication before the player is even loaded. The most effective method is to integrate this portal with a corporate Single Sign-On (SSO) solution, such as Azure Active Directory or Okta. When an employee attempts to view the stream, they are redirected to their standard corporate login page. Upon successful authentication, the SSO provider passes a secure assertion back to the video portal, granting access. This ensures that only current, authenticated employees can view the town hall, and access is automatically revoked when an employee leaves the organization. This SSO-gated approach is vastly superior to simple password protection for the video stream.
Auditing and Compliance Logging for Singaporean Enterprises
For any enterprise operating in Singapore, comprehensive logging is essential for PDPA compliance and internal security audits. A professional E2EE workflow provides detailed logs at every stage. The contribution encoder logs the SRT connection status, including handshake success/failure and encryption status. The cloud media platform logs every ingest attempt and transcoder activity. The CDN provides detailed analytics on every viewer session, including IP address, geographic location, and playback duration. The secure video portal logs every authentication attempt via the SSO integration. This complete audit trail allows an organization to demonstrate due diligence in protecting sensitive corporate data and provides invaluable information for forensic analysis in the event of a suspected security incident.
Actionable Recommendations for a Secure Production Workflow
To successfully implement an E2EE strategy for a corporate town hall in Singapore, production managers and IT directors must collaborate on a unified security posture. First, mandate the use of the SRT protocol with AES-256 encryption for all video contribution feeds originating from the event venue or remote locations. Second, deploy a fully segmented production VLAN on-site with strict firewall rules and no access to or from the general corporate network. Third, invest in and utilize only professional-grade hardware encoders and decoders that have proven, reliable implementations of secure transport protocols. Fourth, partner with a video platform and CDN provider that offers a full suite of security features, including SSO integration, tokenized URLs, and DRM. Finally, conduct a full threat model analysis before each major event to identify and mitigate potential vulnerabilities in the end-to-end signal chain. By adopting these broadcast engineering and cybersecurity principles, organizations can ensure their most critical internal communications remain confidential and secure.
