 March 5, 2026 by Editor |
March 5, 2026 by Editor |
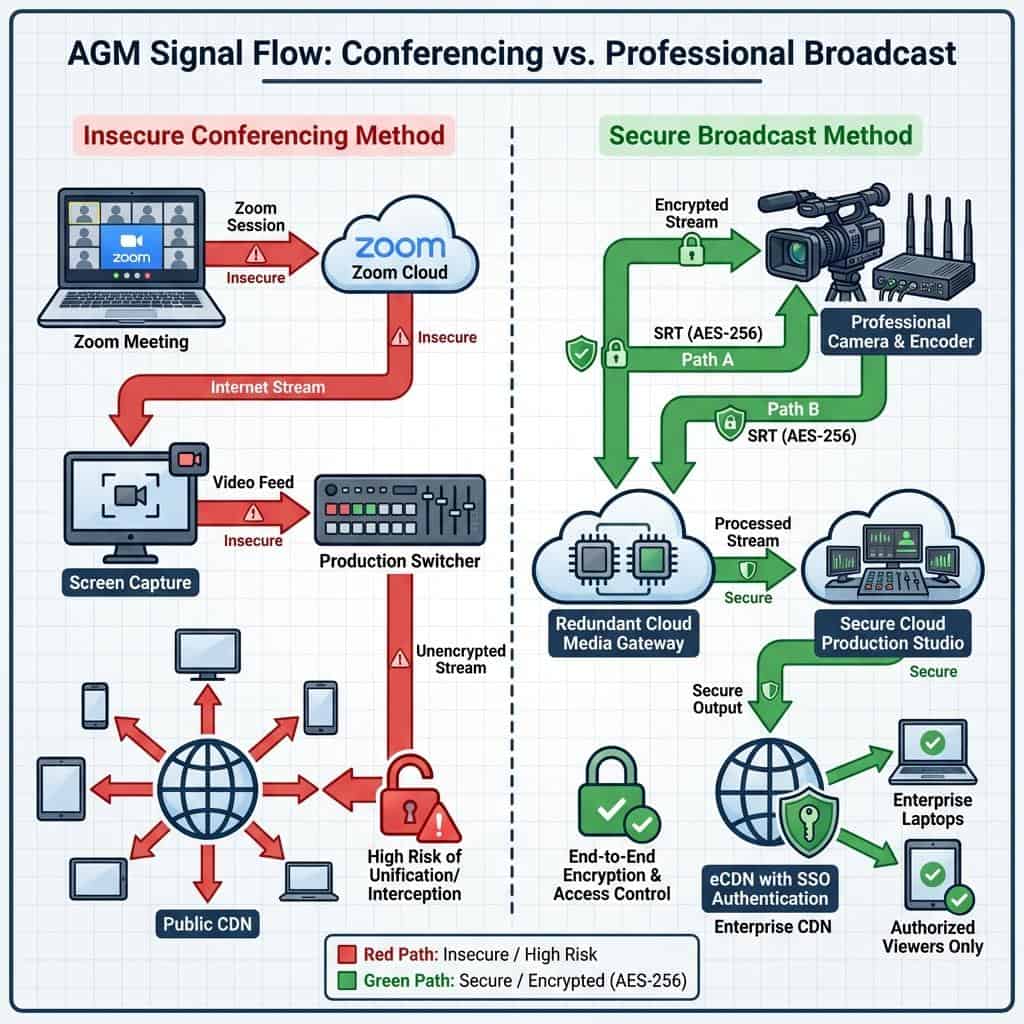
For enterprise-level events like Annual General Meetings (AGMs), the stakes are extraordinarily high. These are not just internal updates; they are legally mandated assemblies where shareholder data, voting integrity, and executive communications must be handled with broadcast-level precision and ironclad security. In this context, relying on the same consumer-grade video conferencing tools used for daily team check-ins, such as a standard in-house Zoom call, introduces a spectrum of technical and security risks that are simply unacceptable. The architectural paradigm of a conversational platform is fundamentally misaligned with the requirements of a secure, one-to-many broadcast event. This is not an issue of quality alone; it is a critical matter of corporate governance, data protection, and risk mitigation. Moving from a makeshift conferencing setup to a professional streaming architecture involves a deep understanding of signal flow, encryption protocols, and production infrastructure designed for resilience and control.
The Fundamental Architectural Mismatch: Conferencing vs. Broadcasting
The primary point of failure when using platforms like Zoom for high-stakes events stems from their core design philosophy. These are collaboration platforms, optimized for low-latency, multi-point, peer-to-peer style communication. A professional broadcast or streaming event, however, operates on a contribution and distribution model, a linear workflow engineered for control, quality, and security from glass to glass.
Peer-to-Peer vs. Contribution and Distribution Models
A standard Zoom session operates on a distributed model where each participant’s client is a potential source and destination, managed by Zoom’s cloud infrastructure to optimize real-time interaction. This is efficient for conversation but creates a chaotic and uncontrollable production environment. A professional event workflow is strictly hierarchical. It begins with the contribution phase, where high-quality audio and video sources are ingested into a central production environment. This is achieved using robust contribution protocols like Secure Reliable Transport (SRT), which provides low-latency, high-quality video transport with AES-256 bit encryption over unpredictable public networks. The signal from a CEO’s remote location is not just another box in a gallery view; it is a dedicated, secure feed sent from a professional hardware encoder to a specific ingest point. This central production hub, whether an on-premise control room with Serial Digital Interface (SDI) routing or a cloud-based switcher, is where all sources are mixed, graphics are added, and the final program feed is produced. From there, the stream moves to the distribution phase, pushed via Real-Time Messaging Protocol (RTMP) or SRT to an Enterprise Content Delivery Network (eCDN) designed to handle secure, large-scale delivery with granular access control.
Data Handling and End-to-End Encryption in a Production Environment
While video conferencing platforms tout End-to-End Encryption (E2EE), this security layer is often misunderstood and misapplied in a production context. The E2EE promise of Zoom applies between the Zoom clients themselves. The moment that video feed is brought into a professional production workflow, that encryption is terminated. If a production team is using screen capture or even a software solution like Network Device Interface (NDI) to pull a Zoom feed into a switcher like vMix or a Blackmagic Design ATEM, the feed is decrypted and sent in the clear on the local network. This creates a significant security vulnerability. A true broadcast security model maintains encryption throughout the signal chain. An SRT feed from a remote presenter remains encrypted from the hardware encoder all the way to the cloud or on-premise SRT gateway. Within the production environment, signals are managed in a secure SDI or NDI-based infrastructure. When sent for distribution, the stream is re-encrypted via RTMPS or another SRT layer to the eCDN, which then manages secure delivery to authenticated viewers. This ensures there is no unencrypted point of vulnerability for a man-in-the-middle attack within the production pipeline.
Ingress and Egress Vulnerabilities in a Makeshift Workflow
Using a consumer platform for a professional AGM forces production teams to adopt insecure and low-quality workarounds for signal ingress (getting sources into the production) and egress (delivering the final program). These workarounds represent the most significant points of technical failure and security exposure.
Uncontrolled Participant Endpoints
In a standard Zoom call, every remote participant is an island of technical uncertainty. Presenters join from unmanaged personal laptops, on consumer-grade networks, using built-in webcams and microphones. The IT or production team has zero control over their device’s security posture, background applications consuming CPU and bandwidth, or the quality of their connection. This leads to common issues like unstable video, robotic audio, and potential for malware on the presenter’s machine to compromise the session. The professional solution is to remove this uncertainty. For key presenters, a pre-configured remote production kit, or “fly-pack,” is deployed. This kit contains a professional camera, microphone, lighting, and most importantly, a hardware encoder (e.g., a Haivision Makito X4 or a Kiloview E-series). This device takes a clean HDMI or SDI feed, encodes it to a high-quality H.264 or H.265 stream, and transmits it via the encrypted SRT protocol. This provides a stable, high-bitrate, secure, and fully manageable video source for the production team.
The Screen Scrape Catastrophe: Quality and Security Breakdown
The most egregious technical compromise in using Zoom for a broadcast event is the “screen scrape.” This involves pointing a capture tool at the Zoom application window to get the video into a production switcher. This method is a technical disaster. Firstly, it results in a massive quality degradation; you are capturing a re-compressed video feed that is subject to the resolution and frame rate of your monitor, not the original source. Secondly, it inevitably includes unwanted user interface elements, such as name overlays, mute icons, or pop-up notifications from the host machine. From a security standpoint, it’s a catastrophe waiting to happen. An accidental on-screen notification from an email or messaging app could expose sensitive corporate or personal information to the entire AGM audience. A professional workflow completely avoids this by ingesting each remote participant as a discrete, isolated video source. Using SRT gateways or NDI Bridge, each remote feed arrives as a clean, independent input in the production switcher. This allows the technical director to switch between sources cleanly, create professional multi-box layouts, and ensure that only the intended video and audio are ever sent to the program feed. This method provides full ISO recording (isolated recording) of each source for archival and compliance purposes.

Authentication, Access Control, and Data Integrity
An AGM is a private event for registered shareholders and authorized personnel. Securing access and ensuring the integrity of interactive elements like voting are non-negotiable legal and regulatory requirements. Standard conferencing tools lack the robust infrastructure to meet these demands.
Beyond the Waiting Room: True Enterprise Authentication
Features like Zoom’s waiting room and basic password protection are rudimentary controls that are easily circumvented and do not provide an audit trail. For a secure AGM, you need enterprise-grade authentication. This means integration with a Single Sign-On (SSO) provider like Okta, Azure AD, or Ping Identity. Viewers must authenticate against the corporate directory to gain access. Professional event platforms and eCDNs enable this level of security, along with other powerful access control tools. These include token-based authentication, where each viewer is issued a unique, single-use token to access the stream, preventing unauthorized sharing of links. It also includes the ability to enforce geo-fencing to restrict access to specific geographic locations and IP whitelisting to ensure only users on the corporate network can view the stream. This creates a multi-layered security perimeter that is impossible to replicate with off-the-shelf conferencing software.
Securing Interactive Elements: Q&A and Shareholder Voting
The integrity of shareholder participation is paramount. Using a standard chat window for AGM Q&A is a compliance risk. There is no robust moderation queue, no audit trail, and no way to properly vet incoming questions. An auditable, secure shareholder voting process is even more critical. Professional hybrid event platforms are built with these requirements in mind. They feature dedicated, moderated Q&A modules that allow a communications team to review, approve, and queue questions before they are displayed or sent to the presenters. For voting, these platforms integrate with specialized, secure polling and voting systems from providers like Lumi or Broadridge. These systems provide encrypted, auditable, and legally compliant mechanisms for shareholder voting, ensuring that every vote is securely cast, counted, and recorded, maintaining the integrity of the entire AGM process.
Building a Resilient and Secure AGM Streaming Infrastructure
A successful AGM broadcast is not just secure; it is also resilient. The entire infrastructure must be designed to withstand technical failures without interrupting the event. This requires a professional commitment to redundancy at every stage of the signal flow, a concept that is entirely absent from a single video call.
Redundancy by Design: Path and Source Failover
A single Zoom call is a single point of failure. If the host’s internet connection drops, the entire meeting can be disrupted. A professional broadcast architecture is built on redundancy. For contribution, this means using network bonding technology, combining multiple internet connections (e.g., fiber, 5G cellular, satellite) to create a single, robust data pipe for SRT transmission. It also involves path redundancy, sending two identical SRT streams from the encoder over separate networks to two different cloud ingest servers. If one path fails, a media server can perform a hitless failover, switching to the backup stream with no interruption visible to the audience. This redundancy extends to the production environment, with backup switchers, encoders, and power supplies (Uninterruptible Power Supply, UPS) ensuring the core of the operation remains online.
The Role of the Enterprise Content Delivery Network (eCDN)
Distributing a high-quality video stream to thousands of employees or shareholders simultaneously can cripple a corporate network. Simply sending everyone a link to a public stream (like one from Zoom) results in every individual viewer pulling a separate, high-bandwidth stream from the public internet, a scenario known as a “WAN hairpin.” An eCDN solves this problem. Platforms from vendors like Kollective, Ramp, or Hive integrate directly into the corporate network. The eCDN pulls only a single copy of the live stream from the source and then uses a peer-to-peer or multicast system to efficiently distribute it behind the corporate firewall. This drastically reduces external internet bandwidth consumption. Furthermore, an eCDN provides detailed, real-time analytics on viewer engagement and Quality of Service (QoS), allowing IT teams to monitor network performance and ensure a smooth viewing experience for all participants while maintaining the highest level of security and control over the content delivery.
