 March 22, 2026 by Editor |
March 22, 2026 by Editor |
The Criticality of Secure Q&A in High-Stakes Corporate Events
In the domain of B2B event streaming and hybrid productions, the integrity of the communication channel is paramount. For high-stakes events such as all-hands meetings, shareholder briefings, or sensitive product launches, the interactive Q&A segment represents the point of maximum vulnerability. An unsecured Q&A channel is not merely a technical oversight; it is a significant corporate risk, exposing the event to data leakage, brand damage, and the injection of malicious content. Preventing unauthorised access is a complex, multi-layered challenge that extends far beyond simple password protection. It requires a robust technical framework built on secure network architecture, cryptographic protocols, and meticulously designed production workflows. This is not about filtering spam; it is about implementing enterprise-grade security protocols to safeguard mission-critical communication, ensuring that only authenticated, authorized participants can interact, and that all interactions are managed within a secure, auditable production environment.
The transition to hybrid event models, integrating remote presenters and geographically dispersed audiences, has exponentially increased the attack surface. A producer’s responsibility now encompasses securing endpoints in uncontrolled environments, managing data flow across public and private networks, and integrating disparate platforms, each with its own security posture. This requires a shift in mindset from traditional AV setup to a broadcast cybersecurity paradigm. We must architect systems that assume a threat exists and build in defenses at every stage of the signal and data chain, from the attendee’s client device to the on-premise production switcher and out to the global Content Delivery Network (CDN). The goal is to create a seamless, impenetrable barrier that protects the conversation without hindering legitimate, controlled participation from stakeholders.
Foundational Security: Network and Platform Architecture
The first line of defense in any secure Q&A protocol is the underlying infrastructure. Before a single question is submitted, the network and the streaming platform must be configured to create a hardened, access-controlled environment. This foundational layer dictates the security ceiling for the entire event production.
Hardening the Production Network Perimeter
The on-site production network cannot be treated as a standard corporate LAN. It is a mission-critical broadcast environment that demands isolation and strict access control. The primary strategy is network segmentation using Virtual Local Area Networks (VLANs). At a minimum, traffic should be segregated into distinct VLANs: one for production equipment (switchers, encoders, cameras, NDI traffic), one for control surfaces and management interfaces, another for guest or audience-facing services, and a completely separate one for secure communications like production talkback and IFB systems. This segmentation prevents a compromise in a less secure segment, like guest Wi-Fi, from propagating to the core production hardware. All inter-VLAN routing must be governed by stringent firewall rules, permitting only essential traffic on specific ports. For instance, NDI (Network Device Interface) traffic should be confined to its VLAN, while API calls from a graphics engine to a cloud moderation platform should be explicitly whitelisted at the firewall.
Secure Contribution and Distribution Protocols
The video and audio signals themselves must be protected in transit. For stream contribution from the venue to the cloud encoder or media server, the use of RTMPS (Real-Time Messaging Protocol Secure) is the absolute baseline. RTMPS wraps the stream in a TLS/SSL encryption layer, preventing man-in-the-middle attacks. However, for superior performance and security, the industry is standardizing on Secure Reliable Transport (SRT). SRT provides end-to-end AES-128 or AES-256 bit encryption, offering robust protection against eavesdropping. Crucially, it also includes packet recovery mechanisms, making it ideal for transmission over unpredictable networks. Implementing SRT requires compatible hardware or software encoders at the contribution point and an SRT-capable gateway or media server at the destination, creating a secure tunnel for the primary program feed before it even reaches the audience-facing platform.
Platform-Level Access Control and Authentication
The streaming platform itself is the gatekeeper for user access. Relying on simple, shareable passwords is insufficient for corporate briefings. The platform must integrate with enterprise identity providers (IdPs) like Azure Active Directory, Okta, or Ping Identity via Single Sign-On (SSO) protocols such as SAML 2.0 or OpenID Connect. This delegates authentication to the corporate identity system, ensuring that only current, authorized employees or stakeholders can access the event stream and its associated Q&A module. Further layers of control include domain gating, which restricts access to users with a specific corporate email domain, and the use of unique, token-based authentication links that expire after a single use. The platform’s API, which governs the Q&A functionality, must be secured with OAuth 2.0 or a similar framework to ensure that all data submissions are tied to an authenticated user session.
Implementing a Multi-Layered Q&A Moderation Workflow
With a secure foundation in place, the focus shifts to the active management of the Q&A process. A secure workflow is not just about technology; it is an operational discipline that separates roles, creates checkpoints, and ensures no unvetted content ever reaches the live program feed. This requires a deliberate architectural design for the flow of data from submission to broadcast.
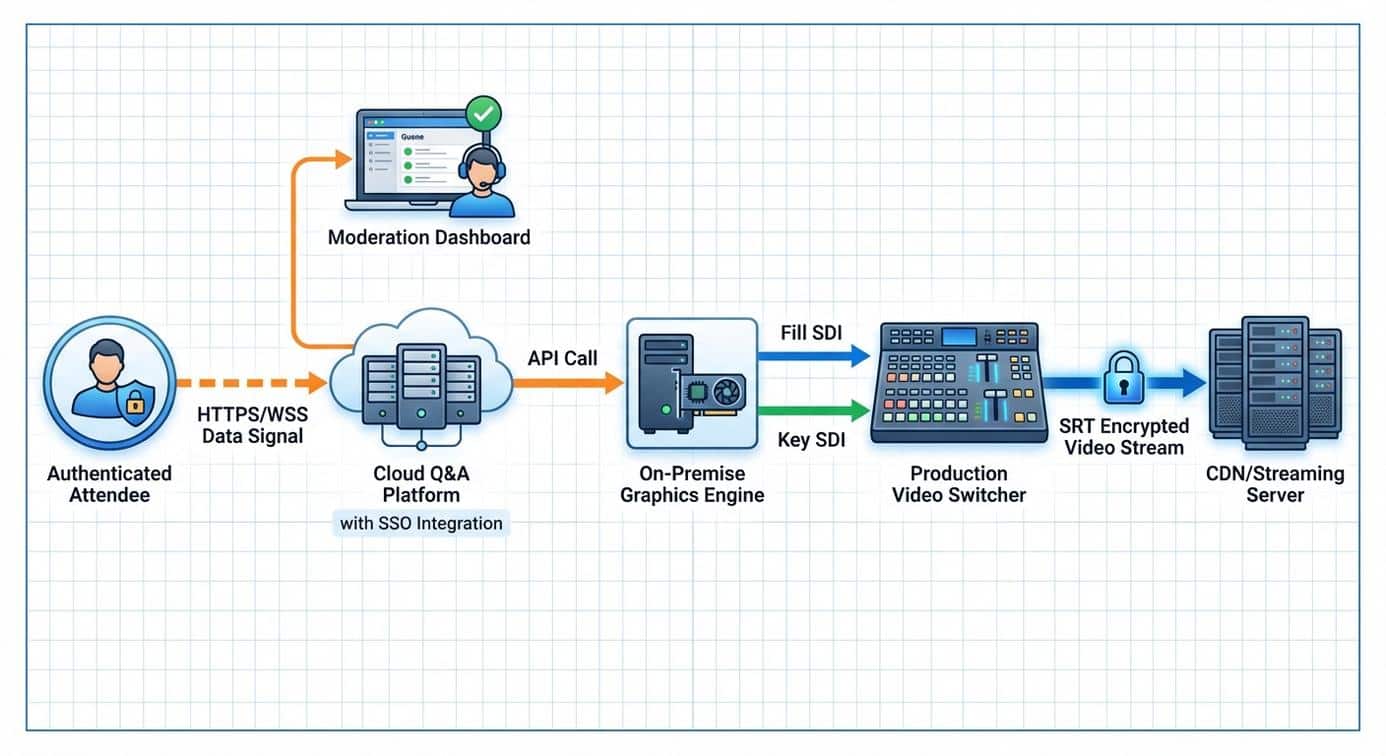
Mapping the Secure Data Flow for Question Handling
The journey of a single question must be meticulously mapped and secured at each step. Step 1: Submission. The authenticated attendee uses a client-side interface (typically a JavaScript module) that communicates with the Q&A platform’s backend via a secure WebSocket or HTTPS POST request. This initial transmission must be encrypted. Step 2: Ingestion and Queuing. The platform’s backend receives the question, associates it with the authenticated user’s ID, and places it into a moderation queue. This entire backend infrastructure should reside within a secure Virtual Private Cloud (VPC). Step 3: Moderation. A designated moderator accesses a separate, secure web-based dashboard. This interface pulls questions from the queue, allowing the moderator to approve, reject, or even edit for clarity. Every action is logged against the moderator’s user ID. Step 4: Integration with Production. Once approved, the question is pushed via API to a graphics rendering engine. This engine generates the visual lower-third or full-screen graphic. Step 5: Broadcast. The graphic is output as a clean video signal (typically via NDI or an SDI fill-and-key signal from a broadcast graphics system like Chyron or Vizrt) and is composited into the main program feed by the technical director at the production switcher.
Role-Based Access Control (RBAC) in the Production Environment
A critical component of this workflow is stringent Role-Based Access Control (RBAC). Different members of the production and event team require different levels of access. An Attendee can only submit questions. A Moderator can view the incoming queue and approve or reject submissions but cannot push a question to the live broadcast. A Graphics Operator or Producer has the permission to take an approved question from the moderation dashboard and trigger its display in the live program feed. Finally, an Administrator can configure the Q&A settings, manage user roles, and access the full audit logs post-event. This separation of duties prevents a single point of failure or a single malicious actor from controlling the entire chain from submission to broadcast. For instance, the presenter should never be their own moderator; their focus must remain on delivery, while a dedicated team manages the inbound communications flow securely backstage.

Securing Remote Contributor Endpoints and Communication
In hybrid events, executives or speakers often join remotely. These remote endpoints are outside the secure perimeter of the main venue and represent a significant security risk. Securing their connection and communication is just as important as securing the main program feed.
Hardening Endpoints for Remote VIPs
A corporate-managed laptop or a dedicated hardware appliance should be the preferred method for remote contributor participation. These devices can be pre-configured with the necessary security policies, firewall rules, and software. If a “bring-your-own-device” (BYOD) policy is unavoidable, the production team must provide a clear set of security guidelines, including the use of VPNs to connect to the corporate network before joining the event platform. The contribution feed from the remote presenter, carrying their camera and microphone signal, must be encrypted. Again, SRT is the ideal protocol for this, providing a secure and reliable link from their location back to the central production switcher or cloud-based vision mixer. This ensures their video and audio feed cannot be intercepted or replaced during transit.
Securing Production Talkback and IFB Channels
Production communications, including talkback for crew and IFB (Interruptible Foldback) for presenters, are often overlooked security vulnerabilities. These channels carry sensitive directorial cues and private conversations. If using Audio-over-IP (AoIP) protocols like Dante on-site, the Dante network must be on its own isolated VLAN, completely separate from other production and corporate data traffic. For remote presenters, providing an IFB feed requires a secure audio-only channel. Sending it over the public internet in the clear is unacceptable. A secure solution involves using an SRT gateway that can carry a low-latency, encrypted audio feed to a dedicated hardware or software decoder at the remote presenter’s location. This ensures that production communications remain confidential and cannot be monitored by unauthorized parties.
Auditing, Redundancy, and Real-Time Mitigation
A truly professional secure Q&A system includes provisions for monitoring, auditing, and recovering from failure. Security is not just about prevention; it is also about detection, response, and resilience.
Comprehensive Logging for Security and Compliance Audits
Every interaction with the Q&A system must be logged immutably. This includes every user login attempt (successful or failed), every question submitted (with user ID and timestamp), and every moderation action (approved, rejected, edited, with moderator ID and timestamp). These logs are invaluable for post-event security forensics to investigate any anomalies. Furthermore, for organizations that must adhere to compliance frameworks like ISO 27001 or SOC 2, these audit trails are non-negotiable. They provide the evidence necessary to demonstrate that robust security controls were in place and operating effectively during the corporate briefing.
Failover Protocols for Mission-Critical Interactivity
Technical systems can fail. The Q&A platform API might become unresponsive, or the on-site graphics generator could crash. A resilient production plan must account for this. The primary failover strategy involves having a secondary, pre-configured Q&A system or workflow ready. This could be a different platform or a simplified manual process. For example, a backup workflow might involve a moderator receiving questions via a secure, end-to-end encrypted messaging app, manually typing the approved question into a prepared graphics template on a separate machine, and feeding that into the switcher. While less elegant, this manual backup ensures the interactive segment of the event can continue in the face of a primary system failure, maintaining business continuity for the briefing. This level of contingency planning is a hallmark of professional B2B event production and a core component of a truly secure Q&A protocol.
