 April 24, 2026 by Michael Koh |
April 24, 2026 by Michael Koh |
In the high-stakes realm of B2B event streaming and hybrid production, the integrity, confidentiality, and availability of content are paramount. Unlike consumer-grade streaming platforms, corporate broadcasting often involves sensitive internal communications, proprietary product launches, financial reporting, and confidential stakeholder engagements. The potential for data breaches, unauthorized access, or signal hijacking carries significant reputational, legal, and financial repercussions. A robust security posture is not merely a best practice; it is an operational imperative. The digital audit, in this context, serves as a comprehensive, systematic evaluation of an enterprise’s live streaming infrastructure, protocols, and workflows to identify vulnerabilities, ensure regulatory compliance, and fortify defenses against evolving cyber threats.
The Imperative of Security in Enterprise Broadcast Ecosystems
Understanding the Threat Landscape in Corporate Broadcasting
The attack vectors targeting corporate broadcasts are diverse and sophisticated. They range from denial-of-service (DoS) attacks aimed at disrupting live events, to man-in-the-middle (MiTM) attacks intercepting unencrypted streams, and unauthorized injection of malicious content. Furthermore, insider threats, though less common, can pose significant risks, especially concerning sensitive data handling and access to production control systems. Exploitable vulnerabilities can reside at various layers of the streaming stack, from encoder firmware and content delivery network (CDN) configurations to authentication mechanisms for viewing platforms and the physical security of production facilities. Enterprise decision-makers, AV professionals, and IT directors must recognize that every component within the broadcast chain, from the initial camera sensor to the final viewer’s screen, represents a potential point of compromise.
Navigating Regulatory Compliance and Data Governance
Corporate broadcasting is increasingly scrutinized under stringent regulatory frameworks. Global data protection regulations such as the General Data Protection Regulation (GDPR), California Consumer Privacy Act (CCPA), and industry-specific mandates like HIPAA for healthcare events or PCI DSS for financial services, impose strict requirements on how personal and sensitive data is collected, processed, and transmitted. An effective digital audit must assess compliance with these regulations, particularly concerning viewer analytics, registration data, and any interactive elements involving personal information. Adherence to international standards like ISO 27001 (Information Security Management) provides a structured approach to managing information security risks. For publicly traded companies, Sarbanes-Oxley (SOX) compliance may also extend to the integrity of financial communications delivered via live streams, necessitating verifiable security controls.
Fortifying the Streaming Infrastructure: Technical Controls and Protocols
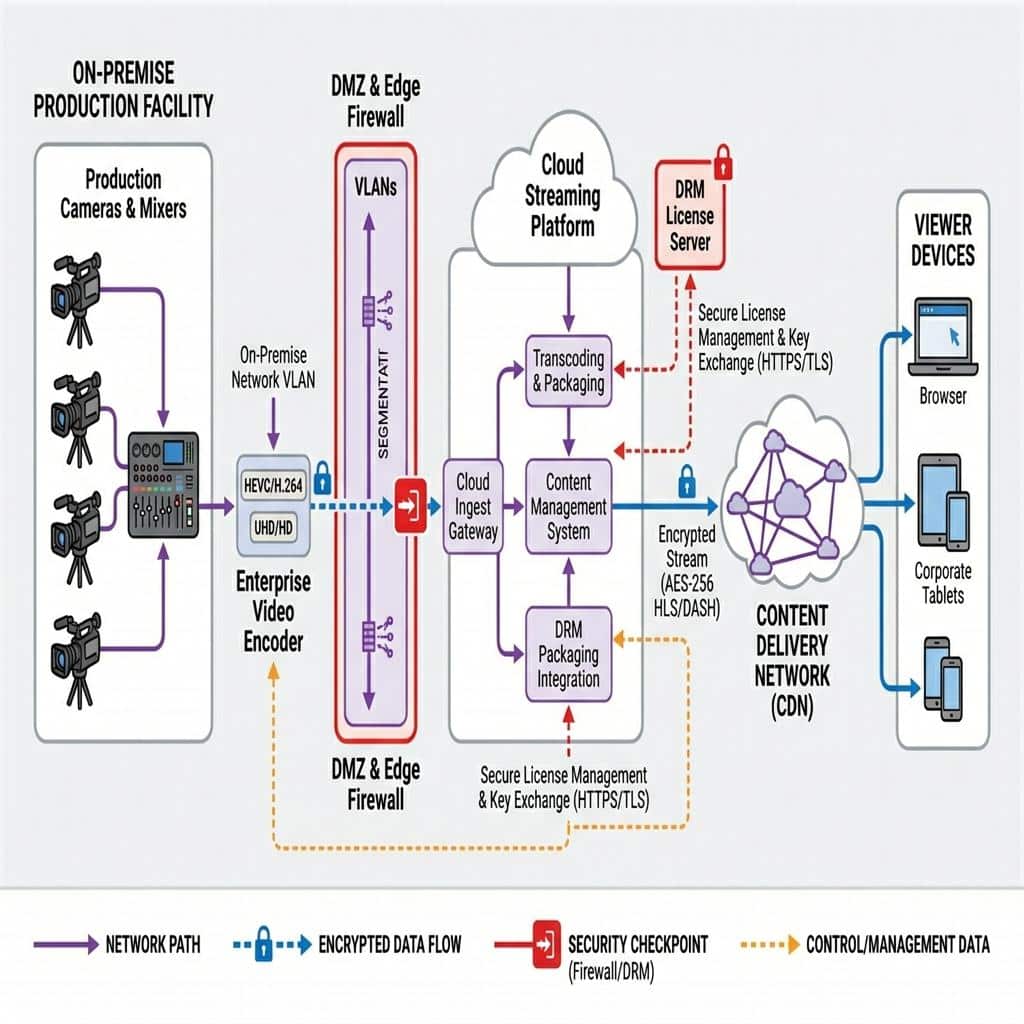
Securing the B2B streaming infrastructure demands a multi-layered approach, integrating advanced technical controls at every stage of the content lifecycle: ingest, transport, processing, and delivery. A thorough digital audit meticulously examines each of these layers.
Secure Ingest and Transport Protocols
The initial ingest point, where raw audio and video signals are encoded and prepared for transport, is a critical vulnerability. Unsecured Real-Time Messaging Protocol (RTMP) streams, while ubiquitous, are susceptible to eavesdropping and manipulation. The industry has largely migrated towards more secure alternatives. Real-Time Messaging Protocol Secure (RTMPS), which encapsulates RTMP within Transport Layer Security (TLS), provides encryption and server authentication. For more demanding, low-latency, and high-reliability scenarios, Secure Reliable Transport (SRT) protocol has emerged as a superior choice. SRT, an open-source video transport protocol, offers robust error recovery, end-to-end encryption (AES-128/256), and dynamic latency adjustment, making it ideal for contribution feeds over unpredictable networks. Network Device Interface (NDI) also offers secure transport options, especially NDI|HX, which leverages H.264 or H.265 encoding with optional encryption for IP-based video production workflows within a local area network (LAN) or across a virtual private network (VPN).
Content Encryption and Digital Rights Management (DRM)
Beyond transport security, content itself must be protected at rest and during playback. Advanced Encryption Standard (AES) encryption, typically AES-128 or AES-256, is standard for protecting video segments. This is commonly implemented with HTTP Live Streaming (HLS) or Dynamic Adaptive Streaming over HTTP (DASH) protocols, where media segments are encrypted and decryption keys are delivered securely via a Key Exchange System (KMS). For premium corporate content or highly confidential broadcasts, Digital Rights Management (DRM) technologies, such as Widevine, PlayReady, or FairPlay Streaming, provide a more robust layer of protection. DRM enforces access policies, prevents unauthorized downloads, and restricts playback to licensed devices or applications. A digital audit verifies the correct implementation and lifecycle management of encryption keys and DRM licenses.
Network Segmentation and Firewall Architectures
Robust network architecture is foundational to broadcast security. Implementing strict network segmentation, utilizing Virtual Local Area Networks (VLANs), is crucial to isolate broadcast-specific network traffic from general corporate IT networks. This minimizes the lateral movement of threats in the event of a breach. Firewalls, both hardware and software-based, must be meticulously configured to permit only essential ports and protocols for streaming operations, employing Stateful Packet Inspection (SPI) and Intrusion Detection/Prevention Systems (IDPS). For hybrid events, secure tunneling protocols like IPsec VPNs or TLS VPNs are indispensable for connecting remote production units or audience members to the core streaming infrastructure, ensuring secure data exchange across disparate geographical locations.
Authentication, Authorization, and Access Control
Rigorous identity and access management (IAM) is paramount. All personnel accessing production systems, streaming platforms, and content management systems must be subjected to strong authentication mechanisms, including multi-factor authentication (MFA). Role-based access control (RBAC) should be meticulously implemented, ensuring that individuals only have the minimum necessary privileges to perform their assigned tasks. This applies to production teams, content managers, and third-party vendors. A digital audit examines user provisioning, de-provisioning processes, password policies, and the effectiveness of single sign-on (SSO) integrations with enterprise directories like Active Directory or Okta. Unauthorized access to mixing consoles, video switchers, or encoder control interfaces could lead to catastrophic production disruptions or content manipulation.
Secure Production Workflows and Endpoint Management
Security extends beyond infrastructure to encompass the entire live production workflow, from camera acquisition to final program feed distribution. Each endpoint and process requires careful consideration.
Hardening Production Systems and Endpoints
Production equipment, including professional broadcast cameras, vision mixers, audio consoles, encoders, and media servers, are specialized computers that require hardening. This involves regularly patching operating systems and firmware, disabling unnecessary services, changing default passwords, and implementing endpoint detection and response (EDR) solutions where feasible. The security configuration of video switchers, matrix routers, and multiview monitoring systems must be reviewed to prevent unauthorized configuration changes or signal routing manipulation. For IP-based production environments leveraging NDI or SMPTE 2110, proper network isolation and access controls are vital to prevent unauthorized access to video and audio streams on the production network. ISO recording systems, which capture individual camera feeds, must also be secured to protect raw, unedited content.
Secure Remote Production and Contribution
The rise of hybrid events has necessitated robust solutions for remote contributors and decentralized production teams. Secure contribution links are essential. This often involves leveraging SRT or RTMPS for remote camera feeds or presenter contributions, combined with VPN connections for secure access to production communication systems (e.g., talkback systems over IP). Cloud-based production platforms, while offering flexibility, introduce a shared responsibility model for security. The audit must ensure that cloud services are configured according to best practices, with secure API integrations, strong access policies, and regular security reviews of vendor compliance. For virtual event platforms (e.g., Microsoft Teams, Zoom, Webex), integration points for streaming outputs must be secured, often leveraging RTMP or SRT ingest from the production encoder rather than direct software screen sharing, to maintain quality and control.
Supply Chain Security in Broadcast
A critical, yet often overlooked, aspect of security is the supply chain. This includes hardware manufacturers, software vendors, and third-party service providers (e.g., CDN providers, cloud hosting partners). A digital audit extends to assessing the security practices of these external entities, reviewing their certifications (e.g., SOC 2 Type 2), and ensuring contractual agreements include stringent security clauses. Vulnerabilities introduced through third-party hardware or software components can undermine an otherwise robust internal security posture. Firmware integrity checks and secure boot processes on critical equipment help mitigate risks from compromised hardware.
The Digital Audit Framework: Methodologies and Continuous Compliance
A successful digital audit is not a one-time event, but an ongoing process integrated into an enterprise’s overall risk management strategy. It combines structured methodologies with advanced tools for continuous monitoring.
Vulnerability Assessments and Penetration Testing
Systematic vulnerability assessments (VAs) are essential to identify known security weaknesses across all network devices, servers, streaming applications, and production hardware. These assessments utilize automated scanning tools to detect misconfigurations, unpatched software, and insecure protocols. Building on VAs, penetration testing (pen testing) goes a step further by simulating real-world cyberattacks. Ethical hackers attempt to exploit identified vulnerabilities to gain unauthorized access, disrupt services, or exfiltrate data. For corporate broadcasting, pen testing scenarios should specifically target the live stream itself, the underlying delivery infrastructure, and access points to the production control environment. This includes testing for buffer overflows in encoders, brute-force attacks on streaming platform logins, and attempts to inject malicious packets into media streams. The findings from these tests provide actionable intelligence for remediation efforts.
Log Management and Security Information and Event Management (SIEM)
Effective logging and monitoring are crucial for detecting security incidents in real time and for forensic analysis post-incident. All relevant devices and applications within the streaming ecosystem – encoders, servers, firewalls, CDNs, streaming platforms, and operating systems – must be configured to generate detailed security logs. These logs should be aggregated into a centralized log management system, often integrated with a Security Information and Event Management (SIEM) platform. A SIEM solution provides real-time analysis of security alerts generated by network hardware and applications, allowing for immediate detection of anomalies such as unusual login attempts, unauthorized access patterns, or sudden changes in stream parameters that could indicate an attack. Rule-based alerts and behavioral analytics within the SIEM are instrumental for proactive threat detection.

Incident Response Planning for Live Events
Despite best efforts, security incidents can occur. A well-defined incident response (IR) plan is critical for mitigating damage and ensuring business continuity during a live broadcast. The IR plan for corporate broadcasting must specifically address scenarios like stream hijacking, content injection, DDoS attacks, and unauthorized access to production control. It should outline clear roles and responsibilities, communication protocols (internal and external), technical containment strategies (e.g., failover to backup streams, network isolation), and post-incident recovery procedures. Regular tabletop exercises and simulations, involving both IT security and production teams, are vital to test the effectiveness of the IR plan and ensure all stakeholders are prepared for potential crises.
Continuous Compliance and Auditing
The threat landscape is constantly evolving, making continuous compliance an absolute necessity. A digital audit should establish a framework for ongoing monitoring and periodic re-evaluation of security controls. This includes automated security checks, regular review of access logs, quarterly vulnerability scans, and annual penetration tests. Policies and procedures related to data handling, access control, and incident response must be reviewed and updated to reflect new technologies and regulatory changes. For enterprise clients, maintaining an audit trail of all security configurations, remediation actions, and compliance reports is essential for demonstrating due diligence to auditors and stakeholders. The objective is to cultivate a culture of security awareness across all departments involved in corporate broadcasting, from content creation to final delivery.
Conclusion: Proactive Security for Uninterrupted Corporate Communications
The digital audit for corporate broadcasting is more than a technical checklist; it is a strategic investment in the resilience and trustworthiness of an enterprise’s most critical digital communications. By meticulously examining every facet of the streaming infrastructure, production workflow, and content delivery mechanisms, organizations can identify and mitigate vulnerabilities before they are exploited. Leveraging advanced protocols like SRT, implementing robust encryption and DRM, segmenting networks, and enforcing stringent access controls are non-negotiable technical requirements. Furthermore, a commitment to continuous monitoring, proactive vulnerability management, and a comprehensive incident response plan ensures that B2B events, hybrid meetings, and internal communications remain secure, compliant, and uninterrupted. For Live Streaming Studio, empowering clients with this level of technical security and operational assurance is fundamental to delivering professional B2B event streaming and hybrid production services that meet the highest standards of integrity and reliability.

Michael Koh is a production specialist and entrepreneur who founded Spring Forest Studio in 2017 to provide event and virtual production solutions in Singapore. He specialises in hybrid live streaming, XR (Extended Reality) virtual production, and studio systems integration, transitioning the business from traditional videography to advanced corporate broadcasting. Operating out of a dedicated facility at NordCom2 in Singapore, he leads a technical crew to deliver multi-camera webcasts, digital sets, and technical consultations for large-scale corporate events.
