 April 16, 2026 by Michael Koh |
April 16, 2026 by Michael Koh |
In the high-stakes world of enterprise communication, the integrity and confidentiality of executive updates are paramount. For corporate event planners, AV professionals, and IT directors, ensuring a secure link for confidential B2B event streaming and hybrid productions is not merely an operational concern; it is a strategic imperative. Unauthorized access, data breaches, and content leakage can have catastrophic consequences, impacting shareholder confidence, market perception, and regulatory compliance. This article delves into the advanced technical methodologies and infrastructure required for managed distribution, focusing on enterprise-grade solutions that guarantee the secure, reliable, and high-quality delivery of sensitive executive communications.
The Imperative of Secure Distribution for Executive Communications
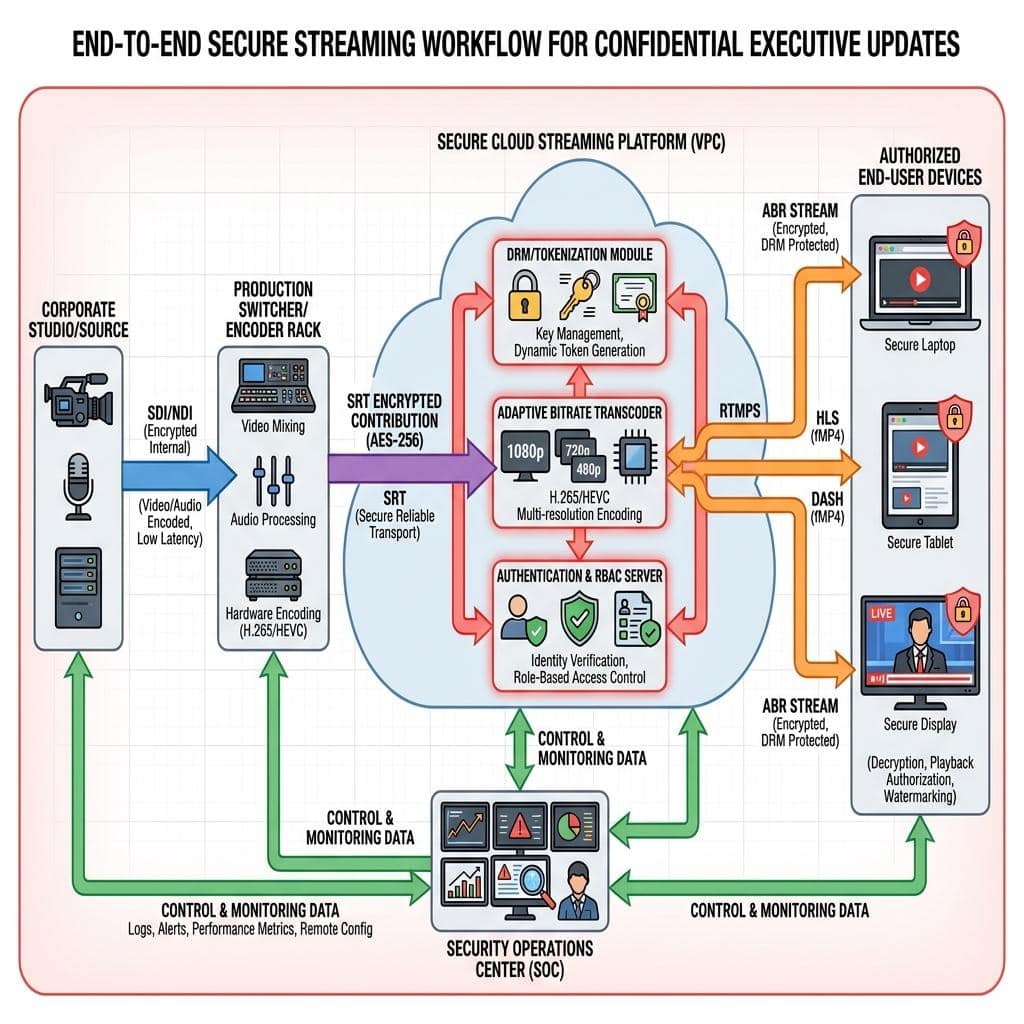
Confidential executive updates, whether quarterly earnings calls, strategic announcements, or internal policy briefings, demand an impenetrable streaming architecture. Unlike consumer-grade streaming, B2B event streaming for confidential content operates under a unique set of constraints, primarily driven by data security, regulatory compliance, and the need for absolute control over content dissemination. The technical challenge lies in creating an end-to-end secure chain, from content acquisition at the source to final delivery on authorized devices.
Threat Vectors in Enterprise Streaming
Enterprise streaming environments are susceptible to various threat vectors that necessitate robust security countermeasures. These include:
- Unauthorized Access: Malicious actors attempting to intercept or view content without proper authentication.
- Data Interception: Eavesdropping on unencrypted or weakly encrypted data streams during transit, potentially compromising sensitive financial data, intellectual property, or strategic plans.
- Content Leakage: Accidental or intentional distribution of confidential material beyond the intended audience, often due to inadequate digital rights management (DRM) or weak access controls.
- Denial-of-Service (DoS) Attacks: Attempts to disrupt service availability, preventing legitimate users from accessing critical updates.
- Replay Attacks: Capturing and re-transmitting legitimate data streams to gain unauthorized access or cause disruption.
Regulatory Compliance and Data Governance
Beyond the immediate security risks, global regulatory frameworks impose stringent requirements on handling sensitive corporate information. Compliance with standards such as ISO/IEC 27001 for information security management, GDPR (General Data Protection Regulation) for data privacy, and specific industry regulations (e.g., SOX for financial reporting) is non-negotiable. An enterprise streaming solution for confidential updates must incorporate technical controls that facilitate auditing, enforce data retention policies, and demonstrate adherence to these legal and ethical obligations. This often involves robust logging, audit trails, and data encryption at rest and in transit.
An effective managed distribution strategy for confidential executive updates mandates a multi-layered security approach, encompassing transport protocols, content encryption, access control, and network segmentation. Without these foundational elements, the risk profile for sensitive corporate communications remains unacceptably high.
Architecting Enterprise-Grade Secure Streaming Solutions
Designing a secure streaming infrastructure for confidential executive updates requires meticulous planning and the integration of advanced technical components. The focus must be on creating a resilient, encrypted, and tightly controlled environment.
Protocol Selection for Confidentiality and Reliability
The choice of streaming protocols is fundamental to ensuring confidentiality and reliability. While RTMP (Real-Time Messaging Protocol) has been a workhorse for ingest, its inherent lack of encryption makes RTMPS (RTMP Secure) a mandatory baseline for any sensitive uplink. However, for true enterprise-grade security and reliability, especially over unpredictable network conditions, SRT (Secure Reliable Transport) is the superior choice. SRT provides:
- End-to-End Encryption: Utilizing AES 128/256-bit encryption, SRT secures the entire path from encoder to decoder, preventing unauthorized interception.
- Packet Loss Recovery: Its advanced ARQ (Automatic Repeat reQuest) error correction mechanism ensures high-quality video and audio transmission even across challenging internet connections, crucial for maintaining production quality in hybrid scenarios.
- Low Latency: Tunable latency settings allow for optimization between speed and reliability, critical for near real-time executive Q&A sessions.
For interactive hybrid event components or peer-to-peer secure communications within a trusted network segment, WebRTC (Web Real-Time Communication) offers encrypted, low-latency browser-based connectivity, typically secured via DTLS (Datagram Transport Layer Security) and SRTP (Secure Real-time Transport Protocol). These protocols form the backbone of a secure and robust distribution network, ensuring data integrity from source to screen.
Encoding and Transcoding for Adaptive Bitrate Distribution
Content encoding and transcoding are not just about visual quality; they are integral to secure delivery. Utilizing robust codecs such as H.264/AVC and increasingly H.265/HEVC for higher efficiency and lower bandwidth requirements, streams must be prepared for adaptive bitrate (ABR) delivery. ABR ensures that viewers receive the optimal quality stream based on their network conditions and device capabilities, without compromising security. This process typically involves encoding the primary program feed into multiple renditions (e.g., 1080p at 5 Mbps, 720p at 2.5 Mbps, 480p at 1 Mbps), each encrypted and protected. Furthermore, integration with enterprise-grade DRM (Digital Rights Management) systems is essential. DRM, such as Widevine, PlayReady, or FairPlay, provides an additional layer of content protection by controlling access and usage rights, preventing unauthorized copying and redistribution of highly sensitive executive content.
Network Segmentation and Firewall Management
A critical architectural component for security is network segmentation. Implementing VLANs (Virtual Local Area Networks) isolates streaming traffic from other enterprise network activities, minimizing potential attack surfaces. Dedicated VPN (Virtual Private Network) tunnels for contribution and distribution paths add another layer of encryption and access control. Sophisticated firewall rules and Access Control Lists (ACLs) must be meticulously configured to permit only authorized traffic on specific ports (e.g., UDP for SRT, TCP 443 for RTMPS) and block all other ingress/egress connections. This level of network hardening is non-negotiable for protecting confidential executive communications.
Managed Production Workflows for Executive Broadcasts
The technical robustness of the streaming infrastructure must be mirrored by equally rigorous production workflows. A managed approach ensures that every stage, from signal acquisition to final distribution, adheres to stringent security and quality protocols.
Multi-Camera Production and Signal Chain Integrity
For professional executive updates, multi-camera production is standard, utilizing high-end broadcast cameras connected via SDI (Serial Digital Interface) for uncompressed, robust signal transmission. A central SDI routing matrix or a sophisticated video switcher manages these feeds, ensuring seamless transitions. For internal IP workflows within a secure studio environment, NDI (Network Device Interface) can be leveraged, but only within carefully segmented networks with appropriate encryption and access controls. Redundant cabling (e.g., dual fiber runs for critical signals) and power supplies are standard practice. Every point in the signal chain, from microphones to audio mixers, and from camera outputs to video switchers and encoders, must be monitored for integrity and potential vulnerabilities. Talkback systems for production crew are segregated to prevent unauthorized listening. The program feed, once composited, is then handed off to secure encoders for distribution.

Secure Cloud vs. On-Premise Hybrid Deployments
The decision between secure cloud-based streaming platforms, on-premise infrastructure, or a hybrid model depends on specific organizational security policies and operational requirements. For highly confidential executive updates, a hybrid approach often strikes the optimal balance. Content can be ingested securely via SRT from an on-premise studio, processed and encrypted further within a private cloud instance or a dedicated virtual private cloud (VPC), and then distributed. This allows organizations to leverage the scalability and global reach of cloud platforms while maintaining maximum control over the most sensitive stages of content handling. On-premise components, such as encoders and local storage, provide an additional layer of control, especially when dealing with data residency requirements or extremely low-latency internal distribution. Cloud platforms must be vetted for ISO 27001, SOC 2 Type II, and other relevant security certifications.
Authentication, Authorization, and Access Control
At the endpoint, stringent authentication and authorization mechanisms are paramount. Implementing SSO (Single Sign-On) integration with enterprise identity providers (e.g., Okta, Azure AD) simplifies access for authorized personnel while centralizing user management. MFA (Multi-Factor Authentication), requiring two or more verification factors, adds a critical layer of security, significantly reducing the risk of unauthorized access due to compromised credentials. Furthermore, RBAC (Role-Based Access Control) ensures that only individuals with specific, predefined roles (e.g., executive, board member, auditor) can access particular content streams or administrative functions. Tokenized access, where a unique, time-limited token is required to view a stream, provides granular control and prevents link sharing. These robust access controls are fundamental to ensuring that confidential information reaches only its intended audience.
Monitoring, Redundancy, and Incident Response
A secure managed distribution system is dynamic, requiring continuous monitoring, built-in redundancy, and a well-defined incident response plan to mitigate risks effectively.
Real-Time Monitoring and Analytics
Comprehensive, real-time monitoring of the entire streaming ecosystem is crucial. This includes network performance (bandwidth utilization, packet loss, latency), encoder health (CPU load, temperature, input signal presence), stream quality (bitrate, resolution, frame rate), and audience engagement metrics. Security logs must be continuously analyzed for suspicious activities, failed login attempts, or unauthorized access patterns. Platforms integrating SNMP (Simple Network Management Protocol) and API-driven data collection can feed into centralized security information and event management (SIEM) systems. This proactive monitoring allows production teams and IT security personnel to identify and address issues before they escalate, ensuring both technical performance and security integrity.
Failover and Disaster Recovery Strategies
Redundancy is a cornerstone of professional B2B streaming, especially for critical executive updates. This extends beyond individual components to encompass entire systems and geographical locations. Implementing geographically dispersed data centers for cloud-based distribution platforms provides inherent resilience against regional outages. Redundant encoders, operating in active/passive or active/active configurations, ensure an uninterrupted program feed. Automated failover mechanisms, meticulously tested during pre-production, can seamlessly switch to backup systems in milliseconds, preventing any disruption to the confidential broadcast. This includes redundant network paths, power supplies, and even backup production teams for high-stakes events. A comprehensive disaster recovery plan, regularly rehearsed, is essential to address unforeseen technical failures or external incidents.
Post-Event Security and Archiving
Security protocols do not cease when the live event concludes. Post-event, all recorded content and associated metadata must be securely archived. This involves encrypted storage solutions, either on-premise or within compliant cloud storage, protected by stringent access controls. Retention policies must be defined and enforced, ensuring that confidential content is stored only for the required duration and then securely deleted in accordance with corporate governance policies. Data sanitization techniques must be applied to storage media to prevent data remnants from being recovered. Secure content delivery networks (CDNs) used for VOD (Video On Demand) distribution of recorded updates must also maintain the same level of encryption and access control as the live stream, typically leveraging DRM and tokenized access for continued protection.
In conclusion, the managed distribution of confidential executive updates demands an uncompromising approach to technical security and operational excellence. From the selection of robust, encrypted streaming protocols like SRT, to the meticulous design of network infrastructure with VLANs and firewalls, and the implementation of advanced authentication and authorization systems, every technical decision contributes to building an impenetrable link. Live Streaming Studio provides the deep technical expertise and infrastructure required to architect, implement, and manage these enterprise-grade streaming solutions, ensuring that your most critical communications remain secure, confidential, and delivered with unparalleled quality to your intended audience.

Michael Koh is a production specialist and entrepreneur who founded Spring Forest Studio in 2017 to provide event and virtual production solutions in Singapore. He specialises in hybrid live streaming, XR (Extended Reality) virtual production, and studio systems integration, transitioning the business from traditional videography to advanced corporate broadcasting. Operating out of a dedicated facility at NordCom2 in Singapore, he leads a technical crew to deliver multi-camera webcasts, digital sets, and technical consultations for large-scale corporate events.
