 March 8, 2026 by Editor |
March 8, 2026 by Editor |
For multinational corporations (MNCs), internal briefings are not mere presentations; they are high-stakes events where sensitive intellectual property is disseminated. From unannounced product roadmaps and confidential financial results to critical M&A discussions, the content of these streams represents significant corporate value. A leak can compromise competitive advantage, impact stock prices, and cause irreparable brand damage. Therefore, ensuring the absolute security of the live streaming infrastructure is not an IT preference; it is a fundamental pillar of corporate risk management. Standard consumer-grade streaming platforms or basic password-protected webcasts are wholly insufficient for this level of security. What is required is a broadcast-grade, multi-layered security architecture that protects the signal path from the camera lens to the corporate viewer’s screen, treating the internal stream with the same rigor as a high-value pay-per-view broadcast.
This technical brief outlines the critical components of an ultra-secure streaming workflow designed for internal MNC briefings. We will examine the specific protocols, hardware configurations, and network architectures required to create a fortified environment for your most sensitive corporate communications. The focus is on implementing a zero-trust model across the entire production and distribution chain, ensuring that every component is hardened, authenticated, and encrypted. This is not about building a wall; it is about building a series of independent, mutually reinforcing security bulkheads from content ingest to final delivery.
The Foundational Layer: Secure Contribution and Ingest
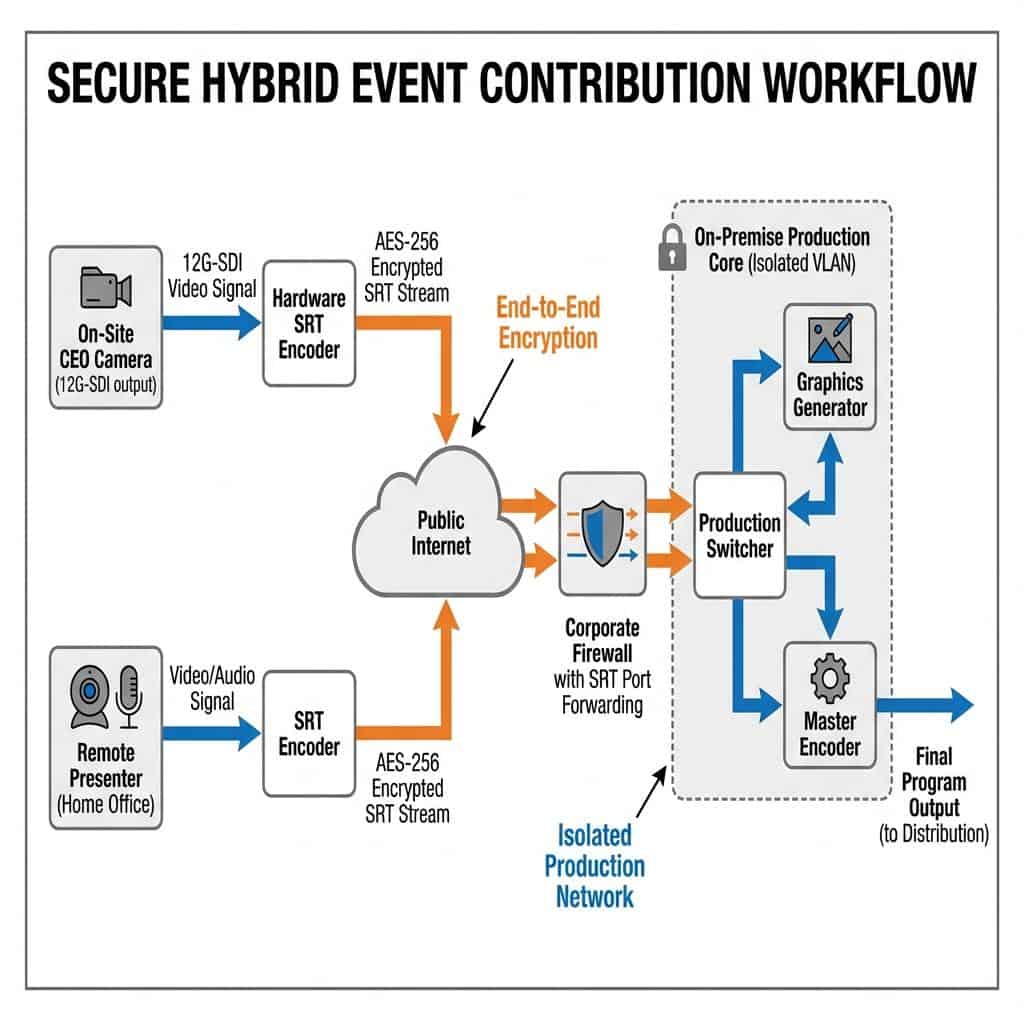
The security of any live stream begins at its point of origin. The contribution phase, which involves transporting the audio and video signals from the source location (e.g., a boardroom, studio, or remote presenter’s location) to the central production facility, is often the most vulnerable link in the chain. Relying on unprotected protocols or public internet connections without adequate encryption is an unacceptable risk for high-value corporate content.
Physical and Network Access Control
Before any data packet is sent, physical and local network security must be established. For on-premise events, this means using dedicated, hard-wired connections for all primary sources. Mission-critical cameras and presentation laptops should be connected via Serial Digital Interface (SDI) or bonded HDMI 2.1 to prevent unauthorized access. The production network itself must be segregated from general corporate or guest Wi-Fi networks. A common best practice is to configure a dedicated Virtual LAN (VLAN) for all production equipment, including cameras, switchers, encoders, and audio mixers. This isolates broadcast traffic and prevents lateral movement from other potentially compromised network segments. Implementing MAC (Media Access Control) address filtering on network switches provides an additional layer of security, ensuring only pre-authorized devices can connect to the production VLAN.
Encrypted Transport Protocols: SRT and RTMPS
When transmitting video over any network, especially the public internet for remote contributors, encryption is non-negotiable. The industry has moved decisively towards the Secure Reliable Transport (SRT) protocol for professional contribution feeds. SRT provides robust end-to-end AES-128 or AES-256 bit encryption, ensuring the stream content is unintelligible to anyone who might intercept it. Its packet recovery mechanism also ensures high reliability over unpredictable networks, which is crucial for maintaining stream integrity. The SRT handshake process requires a passphrase or a secure key exchange, effectively creating a private, encrypted tunnel between the source encoder and the destination decoder or production system. For legacy workflows or platforms that do not support SRT, RTMPS (Real-Time Messaging Protocol Secure) offers a viable alternative. RTMPS wraps the standard RTMP feed in a TLS/SSL session, the same encryption technology used for secure web browsing, providing a secure point-to-point connection. While effective, SRT is generally preferred for its lower latency and superior performance over challenging networks.
Fortifying the Production Core: On-Premise and Cloud Architectures
Once the secure video feeds arrive at the production core, the focus shifts to protecting the content during live switching, graphics insertion, and encoding. The choice between an on-premise and a cloud-based production environment has significant security implications. Both can be secured, but they require different methodologies and expertise to implement correctly.
Secure On-Premise Production Infrastructure
For the highest level of control, a physical, on-premise production control room is the benchmark. This setup allows for a completely air-gapped environment where the production network has no connection to the outside internet. Signal routing is managed by dedicated hardware like a Ross Video Ultrix or AJA KUMO SDI router. The live program is cut on a production switcher, such as a Blackmagic Design ATEM Constellation or a Grass Valley Kula. In this scenario, the only point of egress is the final program feed sent to a dedicated streaming encoder. Control protocols for equipment, like TSL or RossTalk, must operate on a separate, isolated control network to prevent unauthorized access to critical production systems. All multi-view monitors, which display sensitive source feeds, must be located within a physically secure space accessible only to authorized production personnel.
Isolated Cloud Production Environments
While on-premise offers maximum control, secure cloud production is a flexible and powerful alternative. The key is to operate within a Virtual Private Cloud (VPC) on a platform like AWS or Azure. This creates a logically isolated section of the public cloud. Production instances, running software like vMix or OBS Studio, are deployed within this VPC. Network security groups and access control lists are configured to strictly limit inbound and outbound traffic. For example, you can configure rules to only allow inbound SRT traffic from specific IP addresses of your remote contributors. All remote desktop (RDP) or management access must be routed through a secure VPN gateway with multi-factor authentication. This prevents unauthorized access to the virtual production environment while still allowing for remote operation by the production team.

ISO Recording and Secure Asset Management
During production, it is standard practice to create isolated recordings (ISOs) of all camera feeds and the final program output. These assets are as sensitive as the live stream itself. For on-premise productions, ISOs should be recorded to a network-attached storage (NAS) or storage area network (SAN) that utilizes enterprise-grade AES-256 volume encryption. Access to this storage should be tightly controlled via directory permissions. For cloud workflows, assets should be stored in encrypted object storage buckets (like Amazon S3 with SSE-S3 encryption) with strict IAM (Identity and Access Management) policies dictating who can access, modify, or delete the files. A secure post-event media asset management (MAM) plan is critical for archiving, transcoding, or deleting the content according to corporate governance policies.
The Final Mile: Secure Distribution and Access Control
The final and most complex stage is delivering the stream securely to a geographically dispersed internal audience. The distribution strategy must balance scalability, performance, and granular access control to ensure only authorized employees can view the content, and that the content itself is protected from unauthorized recording and redistribution.
Enterprise CDN and P2P Solutions
Broadcasting a high-bitrate 1080p stream to thousands of employees simultaneously can saturate a company’s primary internet connection. An Enterprise Content Delivery Network (eCDN) is essential for solving this challenge securely. An eCDN, from providers like Kollective, Ramp, or Hive, deploys intelligent caching and peer-to-peer (P2P) networking nodes inside the corporate firewall. The primary stream from the production environment hits a central eCDN gateway, which then distributes the stream internally. This dramatically reduces external bandwidth consumption and keeps the majority of stream traffic on the internal corporate LAN/WAN. This architecture is inherently more secure as the content does not have to traverse the public internet to reach the majority of viewers.
Multi-Layered Viewer Authentication
A simple password is not sufficient protection. True enterprise-grade security requires multi-layered authentication tied directly to corporate identity systems. The most robust method is Single Sign-On (SSO) integration with providers like Azure Active Directory, Okta, or Ping Identity. When an employee attempts to access the stream, the video platform redirects them to the corporate SSO portal. The employee authenticates using their standard corporate credentials, often with multi-factor authentication. Upon successful authentication, the SSO provider sends a secure token (SAML or OAuth 2.0) back to the video platform, granting access. This ensures that only current, active employees can view the stream, and access is automatically revoked upon termination. Additional layers like IP whitelisting (restricting access to corporate IP ranges) and geo-fencing (blocking access from specific countries) can further harden the system.
Digital Rights Management and Forensic Watermarking
The ultimate protection against unauthorized copying and distribution is Digital Rights Management (DRM). Enterprise DRM solutions, leveraging native platform technologies like Apple’s FairPlay, Google’s Widevine, and Microsoft’s PlayReady, provide license-based playback control. The video content is encrypted, and a user’s player can only decrypt and play it after receiving a valid license key from a secure license server. This prevents simple stream ripping and downloading. To combat screen recording, forensic watermarking should be employed. Unlike a visible logo, a forensic watermark is an invisible identifier embedded into the video stream that is unique to each viewer’s session. If a recording of the stream appears online, the watermarking can be extracted from the leaked file to identify the exact user session, and by extension the individual, responsible for the leak. This technology serves as a powerful deterrent and a critical investigative tool in the event of a breach. By implementing these advanced measures, MNCs can confidently conduct internal briefings, knowing their most valuable intellectual property is protected by a robust and professionally engineered security framework.
